In this article I describe the Tunneling protocol in computer network for CCNA exam. Tunneling protocol in computer network is related to Link layer of TCP/IP Suite model. The Tunneling protocol in computer network provides the security, encryption, decryption, VPN etc between two different networks on internet. Tunneling protocol in computer network provide the platform for data security at the Link layer of TCP/IP network. The Tunneling protocol in computer network use multiple authentication and encryption of data at internet layer to provide the security to the data packets in the network. Tunneling protocol in computer network also used some algorithms for cryptographic for encryption and decryption of data.
Routing and Routed Protocols provides the connectivity between different networks for data packets flow from one network to another network. A standard routing table is maintained by the routers for data packet flow between different networks.
Before going to learn about Tunneling protocol in computer network in detail, it became helpful to remember the OSI suite and TCP/IP suite model. There are many manufacturer of computer machine in the market. Initially when computers became single user public computer. The computers communicate with only same brand machines. It happens because there was no any fix standard for data transfer between different devices. It is very difficult to make communication with each other when the hardware are of different brands or company. In this article I describe the some basic part of OSI reference layer and TCP/IP Suite model basic concepts in networking with the Tunneling protocol in computer network.
OSI reference model basic concepts
OSI reference model in computer network followed by various vendors to overcome the compatibility problem. After implementation of OSI reference model in computer network, equality maintains by all manufacturer. In 1970 the Open Systems Interconnection (OSI) reference model was created by the International Organization for Standardization (ISO). The OSI model was meant to create inter-operable network with different manufactured devices. In this article I describe some layered approach of TCP/IP Suite model basic concepts in computer network. Before understanding the TCP/IP Suite model basic concepts it is necessary to know about the 7 layers of OSI reference model because the basic work of each layer is described in the OSI reference model. You can read the full article related to OSI reference model in computer networking here.
Importance of OSI reference model for Tunneling protocol in computer network
Before going to know about the Tunneling protocol in computer network at link layer. It is necessary to know the function of layers in OSI model and TCP/IP model. Initially not only hardware but software also not supported for work the different computer brand. It became very difficult for all computer users to working without implementation of OSI reference model in computer network. It is necessary then to make some common protocols for all vendors of computer. Before implementation of OSI reference model in computer network, all vendors implements their own protocols on computer hardware and software.
In networking OSI reference model became helpful. OSI reference model describes the flow of data between nodes in any network. Data from one computer application to another computer application transfer by following some common protocols. The OSI reference layer also become beneficial for troubleshooting the network problems. TCP/IP and Cisco three layered hierarchical model of Cisco became more helpful alongside the OSI reference model.
The Layered Approach in computer network
The Layered approach was the best way to make equality for all computer devices. Layers are not physical but following some protocols. Protocols are for connectivity, connections, data transfer and more. All manufacturer begin to follow the layered approach for OSI reference model in computer network. The OSI reference model change in TCP/IP reference model and later on Cisco three layered hierarchical model. OSI layer architecture have 7 layers. TCP/IP reference model convert these 7 layers into only four layers. After that Cisco three layered hierarchical model converts these 7 layers into three layers. Some layers combined to work in a single layer.
OSI is acronym for open system interconnection. The OSI is a logical reference OSI reference model in computer network. OSI model helps for data flow between different devices and operating systems. All manufacturer used their own architecture before invention of OSI reference model. It was very difficult to establish data communication between different devices. To overcome this problem international organization for standardization (ISO) created the open systems interconnection (OSI) reference model. OSI reference model make data flow possible between different operating system, devices and hardware. Later the OSI model adopted by Cisco as Cisco three layered hierarchical model.
Structure of OSI reference model related to Tunneling protocol in computer network
OSI reference model in computer network consist of 7 layers. These 7 layers further divided into two groups. First 3 layers works for application communication and remaining 4 layers works for data flow. Application, presentation and session layers define the application communication. Transport, network, data link and physical layers define the data flow. Networking protocols works only on last four layers.
TCP/IP Suite model basic concepts for Tunneling protocol in computer network
TCP/IP is acronym for Transmission Control Protocol/Internet Protocol (TCP/IP suite model). In this section of the article I describe about TCP/IP suite model basic concepts in detail. TCP/IP suite model is a reference model like OSI layers. Instead of 7 layers of OSI reference model. TCP/IP suite model consist only four layer. All seven layers are merged into four layers only. TCP/IP suite model was designed and implemented by Department of Defence (DoD). TCP/IP developed to preserve data integrity. The main purpose to develop the TCP/IP is to provide security in the network. A lots of protocols works on each layer to provide a secure network.
It is necessary to understood the protocols used in TCP/IP Suite model basic concepts. IP addressing play an important role in TCP/IP Suite model basic concepts. By using the IP address and subnet masking broadcast domain breaks. It will improve the performance of the network. Breaking broadcast domain increase the data flow speed. Here IP stands for IPV4 only. We ignore the IPV6 for some time in this article. It will make it easy to understand the TCP/IP Suite model basic concepts.
A snap of TCP/IP Suite model basic concepts
In the decade of 1970’s TCP/IP suite model developed by DoD. In the initial stage TCP/IP suite model divided into two segments TCP and IP. Later its name registered with combined name of TCP and IP like TCP/IP model. ARPA, the Advanced Research Projects Agency of DoD officially authorised to use TCP/IP suite model. TCP/IP model was working well so it was adopted by many organisations. In today scenario it is mostly using reference model for networking. Internet is the best example of using TCP/IP.
Process or Application layer of DoD model in TCP/IP Suite model
This is the first layer of TCP/IP of DoD model. It is combination of top three layers of OSI reference model. The functions of Application layer, presentation layer and session layer in OSI model works in single layer process layer. This layer supports the point to point communication and controls the user interface. The data encryption and decryption also done at this layer. Example of some protocols functions at this layer are TLS Transport Layer Security, FTP, LPD, TFTP, SMTP.
Transport layer of DoD model in TCP/IP Suite model
Transport layer of TCP/IP is same as the Transport layer of OSI reference model. It supports the TCP and UDP protocol. This protocol converts the main data segment into packets and transport to the internet layer. The responsibility of Transport layer is to combine the segments and built the data. The data should be reconstruct in its real form. Transport layer is also responsible for creating end-to-end communication between sender and receiver. This layer ensure the delivery of segment in sequence at the receiving device. This property maintains the data integrity.
Internet layer of DoD model in TCP/IP Suite model
Internet layer of TCP/IP is similar to the network layer of OSI reference model. Routing protocols functions on Internet layer of TCP/IP model. Addressing and filtering of packets is main responsibility of Internet layer of TCP/IP model. This layer provides the transmission of packet in the whole network. Some example of protocols functions on internet layer are ICMP, ARP and IP.
Link layer of DoD model in TCP/IP Suite model
Link layer is the least layer of TCP/IP. Basically link layer is combination of data link and physical layer of OSI reference model. Link layer is also known as Network Access layer. It works on MAC address based data transmission. Link layer handles the frame and bits. It receive the bits and constructs frame from merging bits in a sequence. In case of any bit is missing this layer request to re transmit the bits. Ethernet, FDDI, WAP etc functions on this layer. There is no any preset specification for link layer. Link layer functions on any type of existing media.
Tunneling Protocol Explained in brief
Tunneling protocol works at link layer in TCP/IP model. Tunneling protocol configured in routers. Router creates inter-networking between different networks. Tunneling protocol used to flow the data between two routers in encrypted format. Various methods and protocols are used for data encryption and decryption.
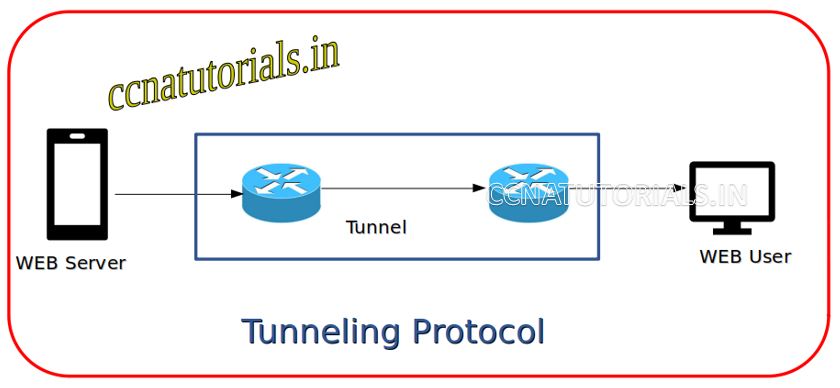
Tunneilng protocol allow private network communication via public network communication. Intranet is the example of use of tunneling . Many companies uses the data communication between too far away locations by using tunneling . Data encapsulation used for transfer the data in encrypted format via internet.
Payload is a part of data packet flowing in a network. Payload consist the main information of data. The Payload doesn’t include the IP header or any addressing protocol. Payload portion carry by the tunneling . The payload data encrypted at the sending host and decrypt at the receiver host. Remaining routing information remain in header portion.
Function of tunneling protocol
Private corporate sector mostly used the tunneling protocol between various location. Data security and integrity is achieved by tunneling on public network. Here public network is internet. Internet can be used by any person or device who is connected with internet. Tunneling creates private network over the public network. Example of tunneling protocol is VPN on internet.
virtual private network is established via tunneling . Preshared key phrase used at both sender and receiver end. The preshared key is unique for every connection. Since the preshared key phrase is not available on any other device, the data can not be decrypt by other devices. Data became secure when transfer from one host to another host using tunneling .
Connection can be establish at via L2TP. L2TP stands for Layer 2 Tunneling Protocol. L2TP allows frame transfer between two nodes on internet. SSH is another way to enable tunneling protocol between two nodes. SSH use port 22 for data encryption which is require to transmits over public network. Tunneling always configured on public network like Internet. Another protocol IPsec provides end to end transfer data. IPsec can be use in a tunneling mode via a security gateway.
SSH Secure Shell Tunneling protocol in computer network
SSH tunnel bypass the firewalls. Firewall restrict the data pass through it for many internet services. Traffic flow on port 80 via using HTTP services are mostly blocks on firewall. SSH allow the same service passes through firewall. SSH clients allow dynamic port forwarding which creates SOCKS 4/5 proxy. User can create an SSH tunnel by using the local SOCKS proxy server. SSH allow to create the tunnel at layer 2 or 3. A virtual interface created on both ends during making connection.
SSH Secure Shell explained in brief
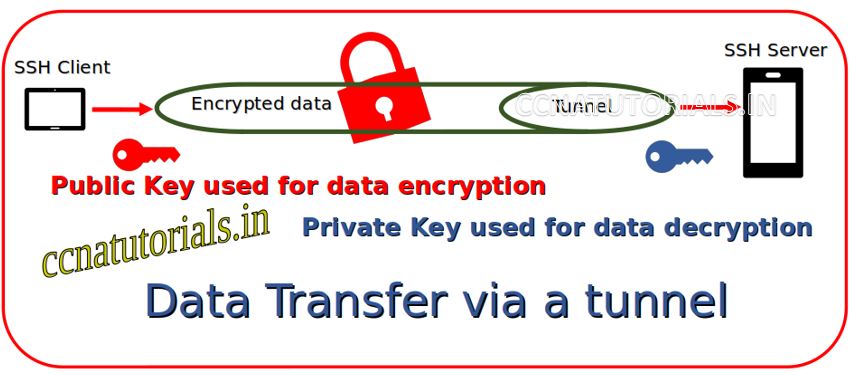
SSH is abbreviation of Secure Shell. SSH Secure shell is an application layer protocol in TCP/IP model. Tht SSH used frequently in the Tunneling protocol in computer network. The SSH Secure shell provides the facility to configure and monitor the remoter servers over the TCP/IP network. Secure shell SSH uses multiple encryption technologies to provide secure connection between the user and remote server. Multiple authentication techniques used by Secure shell. SSH protocol is a remote administration protocol. SSH provides a mechanism for authenticating a remote user with secure username and password. Protocol SSH allow a user to transfer the input from the client to the host.
Symmetric Encryption, Asymmetric Encryption, and Hash technique used for encryption on Secure Shell SSH protocol. SSH uses different type of data manipulation for making secure connection between client and server. SSH works on port number 22 in a TCP/IP network or internet.
Symmetrical Encryption technique for SSH for Tunneling Protocol
The encryption and decryption of data is depending on the encryption scheme. Symmetrical encryption is a kind of encryption scheme which allow data encryption and decryption. In symmetrical encryption a common key is used by the client and server. The key uses to encryption and decryption message of participants. Any client or server can communicate with each other securely by using the common key. Only one single key can be used for all operations of Secure Shell protocol. The secret key generated by key exchange algorithm process. By exchange algorithm both client and server get the common key. Symmetrical encryption is two-way data transferring technique.
Secure Shell protocolconfigured to use different symmetrical cipher systems. The Secure Shell SSH supported by both server and client. Secure Shell supports Windows and Linux environment. Secret key can be generated by using putty software in windows.
Asymmetrical Encryption technique for SSH for Tunneling Protocol
Asymmetrical encryption uses to send data in a single direction either client to server or reverse. In asymmetrical encryption two associated keys required for encryption and decryption. These keys are the private key and public key. Both private key and public key are paired with each other. Public key use to encryption of data. Private key use to decryption of data. It means public key cannot be used for decryption of data. This is why asymmetrical encryption is one-way data sending scheme. The private key never shared with any other client. This means only private key holder can decrypt the data. This feature provides a high-level security feature to SSH protocol. Public key distributed to any client to make SSH connection with the server. SSH key pairs used for authentication of client and server.
In this article I describe the Tunneling protocol in computer network for CCNA Exam. I hope you found this article helpful for any query or suggestions you may drop a comment below or contact us. Your suggestions are always welcome by us.